Guided by MISRA C Working Group chairman and LDRA technical specialist Andrew Banks, LDRA’s new capabilities support embedded developers in aerospace, defense, industrial and energy, medical device and automotive sectors to identify and mitigate potentially dangerous code in increasingly complex and difficult-to-test multithreaded, multi-processor systems.
Introduced in 1998, MISRA C is the standard for developing software in the C programming language where safety, security and code quality are essential. At Embedded World on March 15, the MISRA C Working Group will announce MISRA C:2012 Amendment 4 (AMD4), which specifies rules and directives for multithreading and atomic types as well as clarifications on existing guidance so as to better align with how developers use the C language today.
The group will also introduce MISRA C:2023, which consolidates previous versions of the guidelines into a single, comprehensive edition to facilitate compliance.
“MISRA C guidelines drive the development toward safe, secure and reliable code and this release demonstrates our continued commitment to ensuring MISRA C:2023 compliance is accessible to every safety- and security-critical development team,” said Ian Hennell, Operations Director, LDRA.
“In addition to playing a significant role in developing the guidelines themselves, we have been hard at work ensuring that our static analysis tools include the capabilities necessary to identify, report and remediate critical coding flaws in multithreading, multi-processor systems. These new MISRA additions have made the guidelines even more relevant for developers of embedded products across myriad industries.”
The evolution of MISRA C and the role of LDRA static analysis tools
Under the stewardship of chairman and LDRA technical specialist Andrew Banks, the MISRA C Working Group has evolved the guidelines over the years to apply to software beyond automotive and address additional security considerations while aligning to newer editions of the C standard, including methods of multithreading and atomic types introduced in ISO/IEC 9899:2011 and 2018 (more colloquially known as C11 and C18).
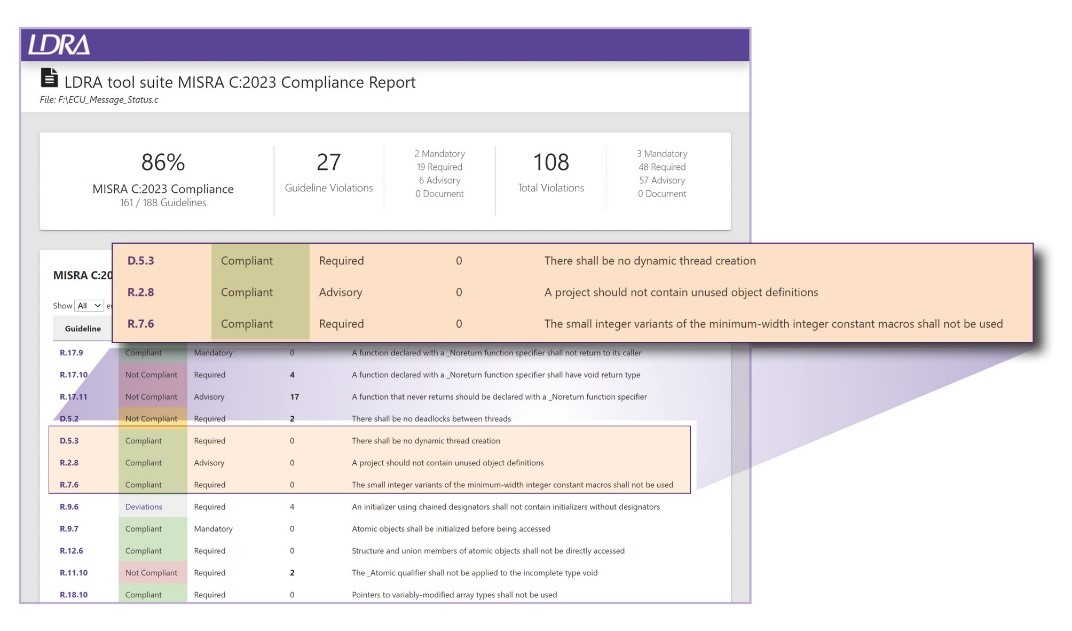
MISRA C guidelines recommend using static analysis tools to validate code against its rules and directives. With support for all versions of the MISRA guidelines, the LDRA tool suite:
- Employs static analysis to identify areas of non-conformant code to aid documentation and modification.
- Includes extensive reports and graphical displays to enhance understanding of the source code in line with MISRA guidelines.
- Facilitates structural coverage analysis to ensure developers can measure and maintain the amount of tested code, as recommended by the MISRA guidelines.
“Adopting static analysis tools is a valuable investment towards MISRA C Compliance,” Banks said. “Such tools streamline MISRA Compliance efforts and reduce risks in new software development, while supporting developer training on MISRA C. They provide the best option for achieving MISRA Compliance, an integral component of any embedded software certification process.”
“Furthermore, by consolidating the recent enhancements into a single source, MISRA C:2023 provides the new benchmark guidance for developers of safety- or security-related, or indeed any high-integrity, software,” added Banks, who serves on the MISRA C Working Group with LDRA colleague and MISRA C++ Working Group chairman Chris Tapp.