As a result of a significant increase in security attacks and with the EU’s Cyber Resilience Act (CRA) regulations due in 2027, there has been a surge in demand for anti-tamper solutions and renewed interest in security certification.
Understanding security certification levels
Common Criteria (CC) or the Common Criteria for Information Technology Security is the International standard (ISO/IEC 15408) for the security evaluation and certification of IT products. CC is focused on detecting and decreasing security vulnerabilities.
There are several levels of vulnerability assurance defined as part of the EAL (Evaluation Assurance Level), and the AVA_VAN (Vulnerability Assessment/Vulnerability Analysis) requirements.
The higher the AVA_VAN level, the higher the level of assurance that the device can withstand sophisticated, professional-grade attacks. Although there are some regional differences between CC schemes in Europe, Asia and the US, there are Common Criteria Recognition Agreements (CCRAs) between countries.
Each security certification level has a specific set of criteria to evaluate the security features, from basic functionality tests to rigorous, formal verification processes. CC AVA_VAN requirements, levels 3 to 5, involve complex vulnerability assessments, penetration testing, and modelling of possible attack routes.
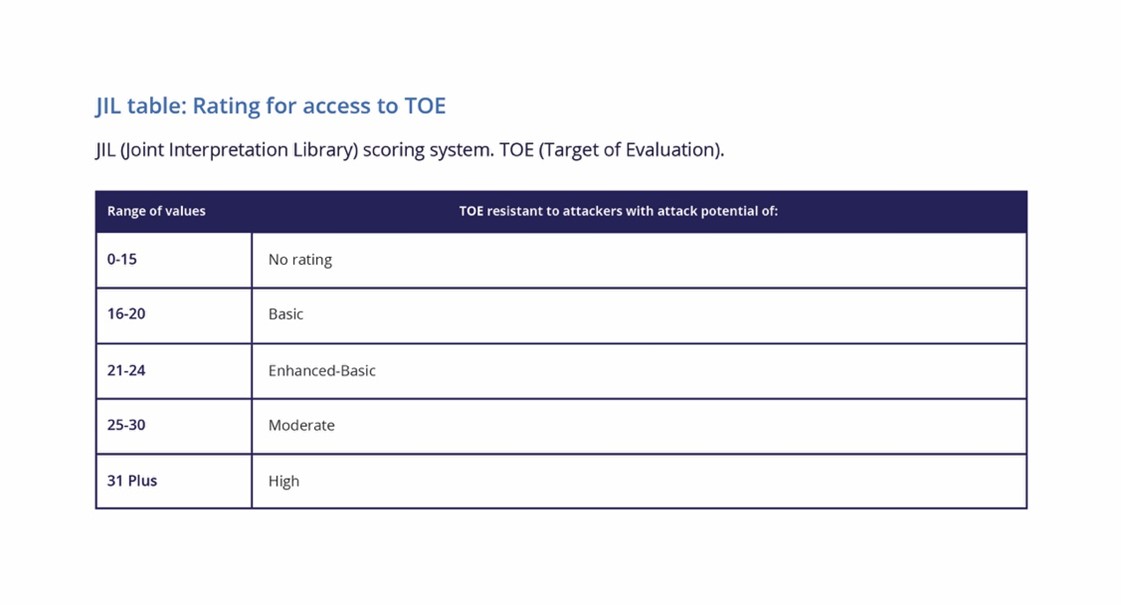
JIL (Joint Interpretation Library) scoring system. TOE (Target of Evaluation).
AVA_VAN.5 is the highest level, demonstrating resistance to attackers with a high security attack potential.
Assessing security attack potential
Each level of AVA_VAN has a different level of attack potential. In the JIL (Joint Interpretation Library) scoring system, at level 3, the attack potential is considered to be Enhanced-Basic.
This is a range of values from 21-24 and is the sum of the identification and exploitation phases of a specific security attack.
In order to reach the level 3 requirement of a range of 21-24, the first consideration is the time the attacker needs to identify and exploit each possible vulnerability. At this level, over a week is 6 points, up to a month is 9 points and over a month is 13 points, for both phases.
Then there is the expertise of the attacker. This should be at least proficient (4 points) or expert (9 points), and the required equipment for the attacker should be categorised as specialised (7 points) or bespoke (11 points).
For an attack by an expert taking more than one week using specialised equipment the attack potential would be rated 22 (6+9+7), which falls within the Enhanced-Basic range of 21-24.
At higher levels of CC (EAL4 and EAL5/5+), the corresponding AVA_VAN.4 or AVA_VAN.5 requirement of resistance to attacks must be met, with corresponding attack potentials of Moderate (25-30) and High (31+).
AVA_VAN.5 is required for EAL5+ certifications, which is the benchmark for secure elements, SIM cards and automotive security chips. Anti-tamper solutions (like voltage and clock glitch monitors) increase the points in these categories, making it take longer or require more expensive equipment, which is how a chip moves from a Moderate to a High rating.
Implementing anti-tamper solutions
Anti-tamper solutions can detect changes that could indicate a possible security attack, such as temperature, voltage, clock frequency, or the presence of an external electromagnetic field.
The integration of these solutions directly impacts on the security certification score. A correctly implemented set of anti-tamper solutions, in our previous example, should extend the attack potential to over a month by an expert with bespoke equipment, achieving a potential score of at least 33 (13+9+11).
Other factors could add to attack potential, like knowledge of the target, access to the target (such as the number of samples required), or a need for open samples to guide the evaluator.
Recent developments mean that there are now anti-tamper IP solutions available that can protect companies against a wide-range of potential security attacks and help achieve higher levels of security certification.
The Agile Analog agileSecure portfolio includes highly configurable anti-tamper security IP solutions. This includes tamper detection IP such as a voltage glitch detector, clock attack monitor, digital temperature sensor, and electromagnetic sensor.
Achieving security certification
Achieving and maintaining a security certification can be technically difficult. The evaluation process is time-consuming and expensive, especially as chip designs are frequently moved to new foundry nodes (or process technologies) to maintain cost and performance advantage.

JIL (Joint Interpretation Library) scoring system.
Agile Analog’s unique technology means that the agileSecure IP can be generated fresh automatically for all major foundries and process nodes and then easily ported as required.
Therefore, applying for and achieving a certification following a port to a new node can leverage much of the prior vulnerability analysis work. This continuity significantly reduces the requirement to re-run extensive penetration testing, improving time-to-market, and cutting development costs.
Paying more attention
With the pressure of new regulations like the Cyber Resilience Act, and the growing complexity and frequency of security attacks, companies across the globe are starting to pay more attention to the issue of security certification.
It is becoming increasingly apparent that novel anti-tamper solutions can be of great benefit, not only for detecting and preventing security attacks, but also as a way to help achieve higher levels of security certification.
This article originally appeared in the March’26 magazine issue of Electronic Specifier Design – see ES’s Magazine Archives for more featured publications.