Security
Security
The risks of public Wi-Fi: a guide to staying secure online
The availability of public Wi-Fi has grown significantly in recent years, with an estimated 628 million public Wi-Fi spots available by 2023.
Fingerprints all-in-one biometric system
Fingerprints unveils FPC AllKey, its new biometric system for logical and physical access control.
International Cyber Expo’s 2024 Tech Hub Stage agenda
Nineteen Group, organisers of International Cyber Expo, has announce the programme for the 2024 Tech Hub Stage.
Cyber experts warn fans about fake Oasis tickets
Major events like the Olympics, Euros, Oasis, and the Eras Tour dominated this summer, bringing with them a new surge in fraudulent activities.
Cyber security's gender divide
The cyber security industry is essential for protecting our increasingly digital world, yet it continues to face a notable gender imbalance.
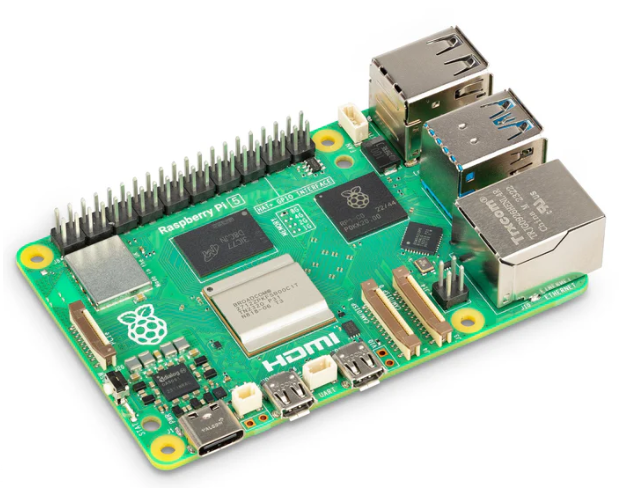
Kali Raspberry Pi – what it is and how it works
Combining Kali Linux with a Raspberry Pi – known as Kali Raspberry Pi – creates a powerful and portable tool for cyber security professionals, educators, and hobbyists.
Can you hack Raspberry Pi’s new chip?
Raspberry Pi has introduced its latest high-performance, secure microcontroller, the RP2350, and is inviting security enthusiasts to put it to the test.
Fabric Cryptography: advanced cryptography with a new kind of chip
As data science and machine learning have become common, users and regulators alike have demanded greater privacy guarantees.
Swissbit debuts iShield Key series at Identity Week America
Swissbit, a provider of storage, security, and embedded IoT solutions, is proud to participate for the first time in Identity Week America 2024, 11–12 September 2024 at the Walter E. Washington Convention Centre in Washington, DC.
NXP delivers customisation for payment cards with JCOP Pay
What’s new: NXP Semiconductors has announced JCOP Pay operating on JCOP 5 EMV, designed to deliver a high degree of customer customisation of payment cards, while simultaneously enhancing their security. With the most recently obtained EMVCo certification, JCOP Pay operating on JCOP 5 EMV enables customers to achieve a long lifetime for card issuance.