The first-ever report on encryption that is based on the views of leading networking vendors finds a strong demand for next-generation DPI solutions that feature encrypted traffic intelligence, with 92.6% of networking vendors having already incorporated the capability, or planning to do so in their existing or future networking or cybersecurity solutions.
Addressing traffic visibility issues from encryption
The research report, entitled ‘Deep packet inspection and encrypted traffic visibility for IP networks’, highlights the impact of newer and tougher encryption protocols such as TLS 1.3, TLS 1.3 0-RTT, and ESNI on network visibility. Visibility loss from encryption is found to be a major concern for 85.3% of vendors, affecting key functionalities such as security, network performance management and analytics. “Loss of traffic visibility can have devastating effects on the network due to heightened vulnerability to security threats, non-optimised management of traffic and poor analytics,” says Dr. Martin Mieth, VP of Engineering at ipoque. “Respondents report more than a third of security incidents to originate from encrypted threats.”
Produced jointly by ipoque and The Fast Mode, a leading telecoms/IT publication, the findings are based on a survey that took place between October to December 2022 and was participated by 34 top-tier networking vendors with solutions spanning network security, network performance management, analytics, policy control and traffic management.
Quest for the ideal tool for analysing encrypted traffic
With decryption methods such as SSL/TLS inspection giving way to security and regulatory pressures, there is an obvious trend towards traffic inspection methods that are less intrusive. Dr. Mieth states, “Vendors are leaning towards methodologies that are no longer dependent on the readability of payload information. In this regard, we note a strong preference for advanced techniques that use behavioural and statistic/heuristic analysis as well as AI-based methods such as machine learning (ML) and deep learning (DL).”
The study underscores the continuous reliance on DPI for real-time network intelligence. “Four-fifths of vendors use or plan to use DPI, with preferences shifting towards turnkey and commercial solutions,” said Ariana Leena Lavanya, Principal Analyst at The Fast Mode. “Admittedly, newer encryption protocols have been progressively eroding the information that is available to DPI tools, but this has become an impetus for DPI vendors to reinvent their approaches, leading to next-gen DPI solutions.”
Next-gen DPI solutions
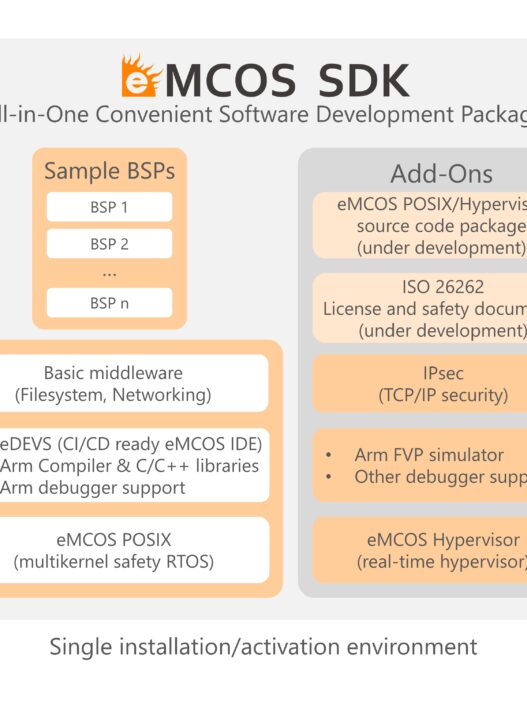
Accelerating the industry’s effort in this area, ipoque introduced encrypted traffic intelligence (ETI) across its suite of OEM DPI solutions, last year. “At its core, ETI features advanced AI-based analysis using ML, DL and high-dimensional data analysis. This includes ML / DL algorithms such as k-nearest neighbours (k-NN), decision tree learning models, convolutional neural networks (CNN), recurrent neural networks (RNN) and long short-term memory (LSTM) networks that boast over 6,000 features – including statistical, time series and packet-level features,” added Dr. Mieth. “We merge these with statistical and behavioural/heuristic analysis and DNS / service caching to accurately and reliably detect encrypted applications and services”.
ipoque’s DPI product portfolio offers the highest accuracy rate in the industry and delivers environment-dependent packet processing with two distinct DPI engines that can be embedded into any networking or cybersecurity solution – R&S PACE 2 which is aimed for traditional, scalar-packet processing architectures and R&S vPACE which caters for high-speed, VPP-based processing in cloud environments. The ipoque DPI technology identifies and classifies thousands of applications, protocols and service types and extracts metadata in real-time. Supported by weekly signature updates combined with continuous performance and reliability testing, networking vendors are able to deliver application awareness in any part of a network, seamlessly and with scalability.
Further insights
The ‘Deep packet inspection and encrypted traffic visibility for IP networks’ report also includes, among others, analyses of various encryption protocols, long-term effects of visibility loss on network outcomes and DPI deployment preferences among networking vendors. Key requirements for tools used for encrypted traffic visibility are also discussed in detail.