Embedded Linux systems are becoming increasingly common due to their superior accessibility, cost-effectiveness, and customisation.
While easy to use and powerful, they present unique security challenges professionals must address to mitigate data breaches. Understanding common security flaws in embedded Linux systems is crucial for preserving integrity, functionality and confidentiality.
1. Insecure default credentials
Shipping devices with hardcoded or easily guessable default credentials inadvertently enables privilege escalation, dramatically increasing the risk of unauthorised administrative access. Containers connected with overly permissive network policies or default bridge networks are also problematic, as they can lead to unintended data disclosure.
2. Lack of secure boot
A secure bootloader is used for authentication and verification. If integrity failure occurs, it will not load user applications, sacrificing functionality to preserve security. If this process is disabled or compromised, an attacker could load malicious firmware.
3. Privilege escalation
With improperly configured permissions and critical vulnerabilities, users run the risk of running processes with unnecessary root privileges. A security flaw in a single application can compromise an entire device if that application has excessive permissions.
For instance, since the dynamic loader’s code runs with elevated privileges when a local user launches a set-user-ID or set-group-ID program, compromising it enables hackers to escalate privileges. They could exploit a vulnerability in the GNU C Library – which is found in most systems running the Linux kernel – to gain full root privileges on default installations.
4. Outdated software and kernel
The set-it-and-forget-it mentality that has long applied to embedded systems is outdated because modern versions are no longer isolated or used for a single purpose. Outdated libraries and kernels that contain known, publicly documented vulnerabilities are a considerable risk.
5. Supply chain vulnerabilities
While open-source software is accessible and affordable, hackers can easily exploit it. The use of third-party software components with unknown or unpatched vulnerabilities introduces security weaknesses into embedded systems.
The prevalence of embedded Linux systems
The prevalence of embedded Linux in commercial and industrial systems is rising rapidly. According to market research, the European embedded software market is expected to reach $10.78 billion by 2033 – up from $5.74 billion in 2025, which is a compound annual growth rate of 8.2%.
Digitalisation has swept businesses, homes and factories across the United Kingdom. Many have implemented IoT-enabled solutions supported by embedded operating systems (OS) because this technology facilitates device interoperability and real-time data processing.
Globally, there are hundreds of active Linux distributions. Most developers use a Linux-based OS, so nearly half of embedded systems run on it. Given the prevalence of embedded systems in Europe, mitigating common security flaws is critical, especially as more highly regulated, data-intensive industries adopt them.
How to address these security vulnerabilities
Hackers typically do not compromise IoT device security by targeting a single critical vulnerability. Instead, they utilise a series of security flaws to create a viable path to exploitation. To secure embedded systems, professionals must establish comprehensive defences.
Verify digital signatures
To ensure code or data integrity, verifying the signature against the file and confirming the certificate chain are crucial. Professionals can use the digital signature application programming interface, compare the cryptographic hashes against trusted keys or use tools such as the GNU Privacy Guard. If the signature is correct, the software has not been tampered with.
Automate software updates
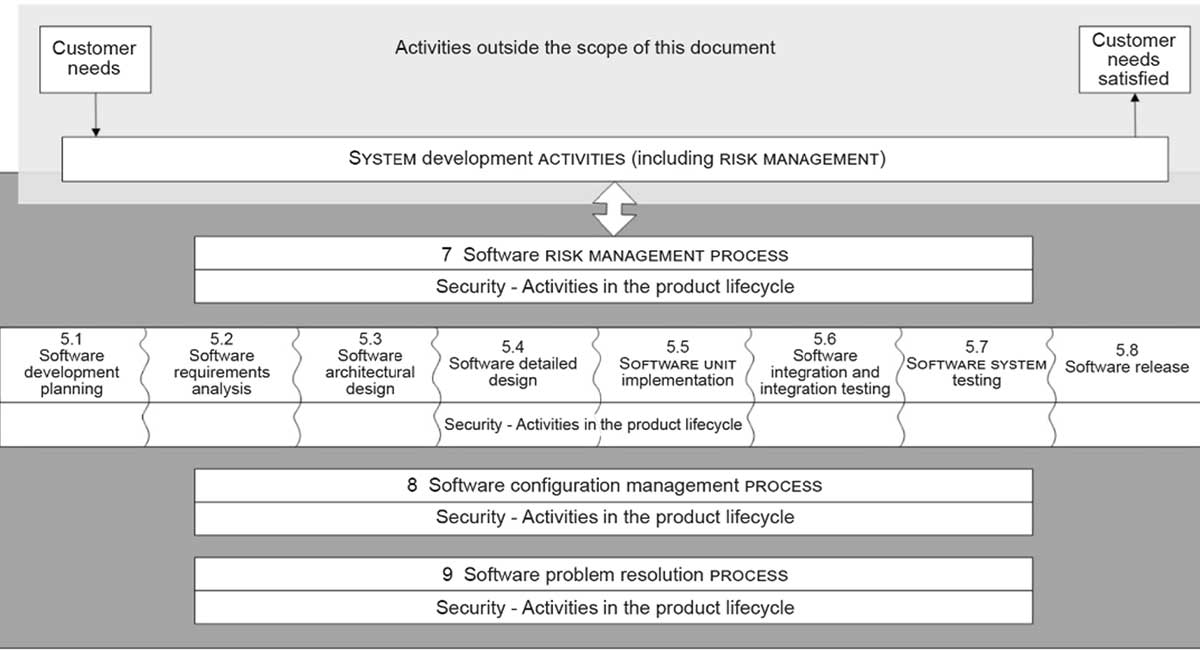
Robust patch management is essential, but many security teams already have large workloads filled with false positives. Automated vulnerability scans and updates are crucial for timely security fixes throughout the device’s life cycle.
Enforce strong passwords and MFA
As information security professionals know, unique passwords should not contain identifiable strings of text. Long sequences of random characters consistently outperform default credentials. However, people do not always follow best practices.
Implementing mechanisms for identity verification can help organisations reduce risk. Research suggests multifactor authentication can stop nearly 100% of account compromise attacks. Even if attackers possess genuine credentials, they are virtually powerless.
Prioritise the principle of least privilege
Applying the principle of least privilege to file systems and processes can help professionals close any remaining security gaps. For instance, they can turn off all nonessential services. There is no one-size-fits-all approach, so they must tailor their strategy to meet the specific requirements of their embedded system and application.
Prevent hackers from compromising systems
Embedded Linux systems lower barriers to entry because they are typically more accessible and affordable than their counterparts. While this is beneficial, it also means end users may not be prepared to handle security risks. Understanding common vulnerabilities can help them ensure the integrity of data and systems.
About the author:

Zac Amos is the Features Editor at ReHack. With over four years of writing in the technology industry, his expertise includes cybersecurity, automation, and connected devices.