The project partners presented the results at the VDMA Forum at SPS, the trade fair for the automation industry.
Under the leadership of Infineon Technologies, the Fraunhofer Institute for Applied and Integrated Security AISEC, Giesecke+Devrient Mobile Security GmbH, Siemens AG, the Technical University of Munich (TUM), and WIBU-SYSTEMS AG have been developing chip-based solutions and prototypes for connected computer applications and embedded systems since 2016.
ALESSIO is supported by around €3.9m in funding from Germany’s Federal Ministry of Education and Research (BMBF) and is scheduled to end on 31st December 2019.
Secure information and communication structures for connected manufacturing
Every new connected device is a potential gateway for cyber attacks. Sensitive company data and information could be captured and misused for further attacks. This is why reliable protection for security-critical information in devices relies on a combination of software and hardware.
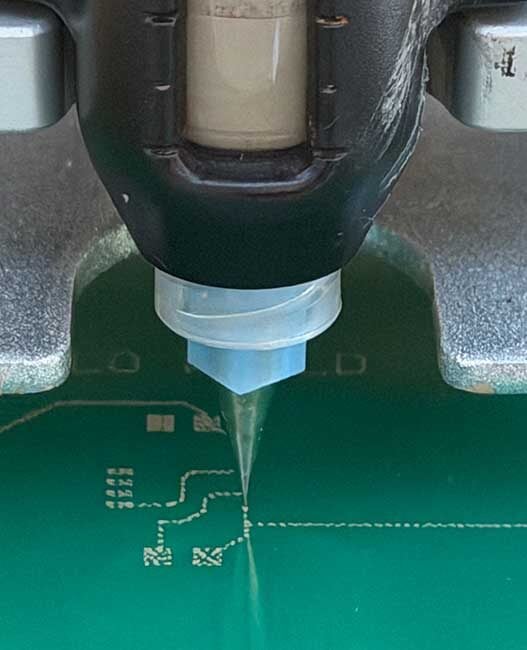
While software can still be modified at a later point, hardware or a security chip, once integrated, is protected from being remotely manipulated. Security chips are comparable to a highly protected area in which data and security-related information are stored separately from the software. Nevertheless, there must also be ways to update this secured area itself, since attack methods may change over time.
The partners on the ALESSIO project were able to show that updatable security solutions can be achieved with two different technical approaches, using either chip-based secure elements with updatable software, or an updatable secure element implemented in programmable logic devices known as FPGAs, in which hardware components can be securely updated during run time.
Both options enable ICT networks and security-related data to be secured and managed efficiently over the long term.